





























Cybersecurity Solutions and Services
Platform-as-a-Service (PaaS)
Resecurity Platform
Next-generation cybersecurity platform designed to detect and mitigate tomorrow’s threats today.

Identity Protection
Identity
Establish maximum protection against digital threats targeting you and your online identity using cutting-edge technology and analytics.
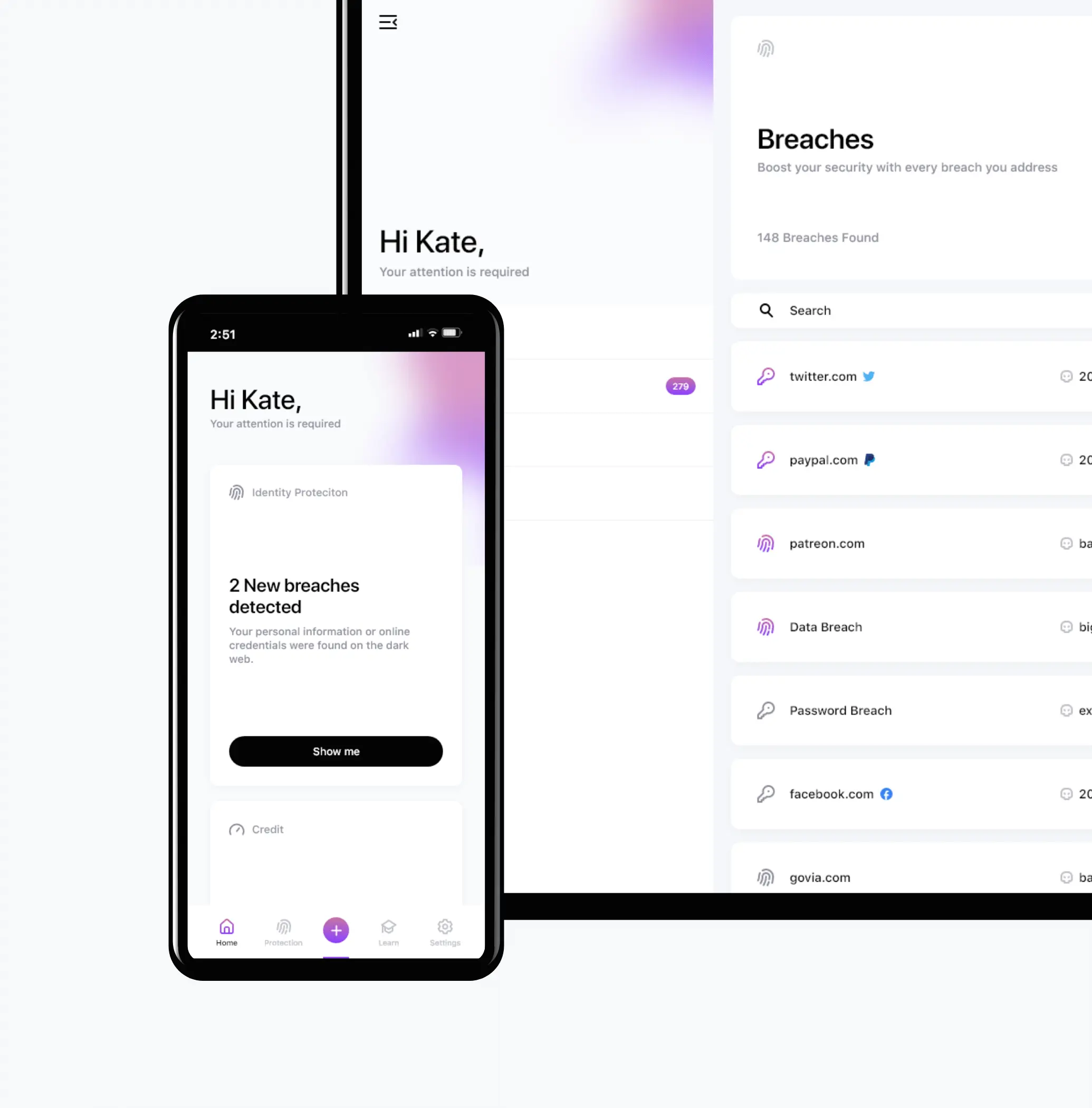
Carry out business as usual with confidence while Resecurity detects, protects, and eliminates any digital threats.
Delivering unparalleled visibility into the most complex threats and security challenges worldwide.
Keep up to date with the latest cybersecurity news and developments.
By subscribing, I understand and agree that my personal data will be collected and processed according to the Privacy and Cookies Policy

Los Angeles, CA 90071 Google Maps




