

Following the recent Twilio hack leading to the leakage of 2FA (OTP) codes, cybercriminals continue to upgrade their attack arsenal to orchestrate advanced phishing campaigns targeting users worldwide. Resecurity has recently identified a new Phishing-as-a-Service (PhaaS) called EvilProxy advertised in the Dark Web. On some sources the alternative name is Moloch, which has some connection to a phishing-kit developed by several notable underground actors who targeted the financial institutions and e-commerce sector before.
While the incident with Twilio is solely related to the supply chain, cybersecurity risks obviously lead to attacks against downstream targets, the productized underground service like EvilProxy enables threat actors to attack users with enabled MFA on the largest scale without the need to hack upstream services.
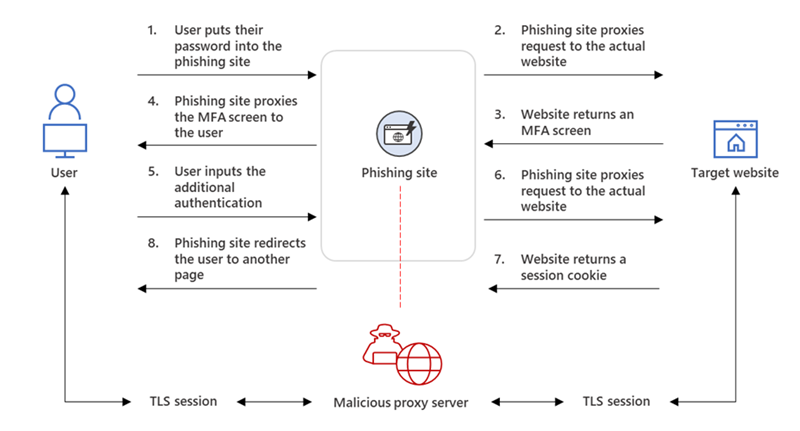
EvilProxy actors are using Reverse Proxy and Cookie Injection methods to bypass 2FA authentication – proxyfying victim’s session. Previously such methods have been seen in targeted campaigns of APT and cyberespionage groups, however now these methods have been successfully productized in EvilProxy which highlights the significance of growth in attacks against online-services and MFA authorization mechanisms.
Based on the ongoing investigation surrounding the result of attacks against multiple employees from Fortune 500 companies, Resecurity was able to obtain substantial knowledge about EvilProxy including its structure, modules, functions, and the network infrastructure used to conduct malicious activity. Early occurrences of EvilProxy have been initially identified in connection to attacks against Google and MSFT customers who have MFA enabled on their accounts – either with SMS or Application Token.
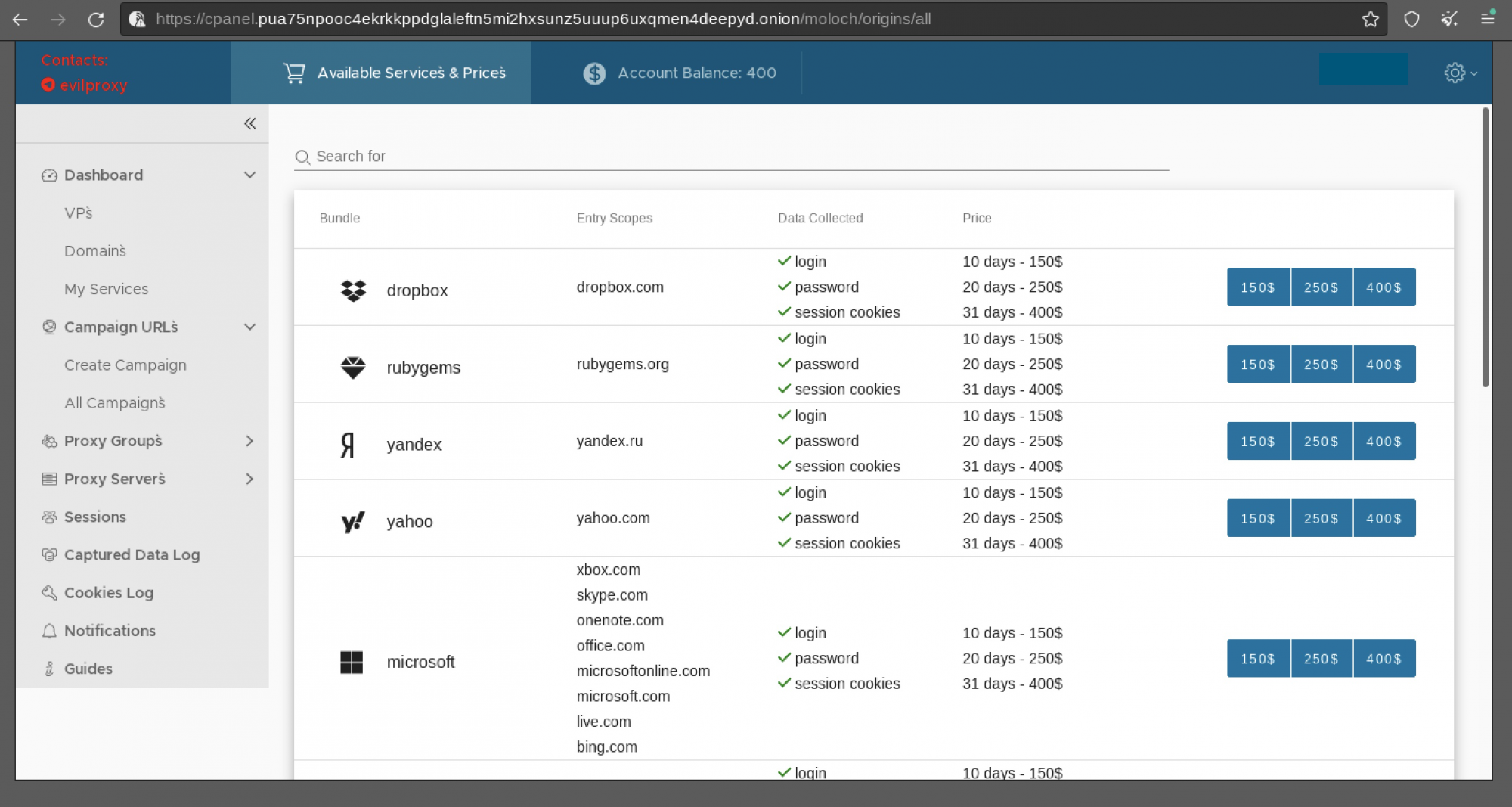
The first mention of EvilProxy was detected early May 2022, this is when the actors running it released a demonstration video detailing how it could be used to deliver advanced phishing links with the intention to compromise consumer accounts belonging to major brands such as Apple, Facebook, GoDaddy, GitHub, Google, Dropbox, Instagram, Microsoft, Twitter, Yahoo, Yandex and others.
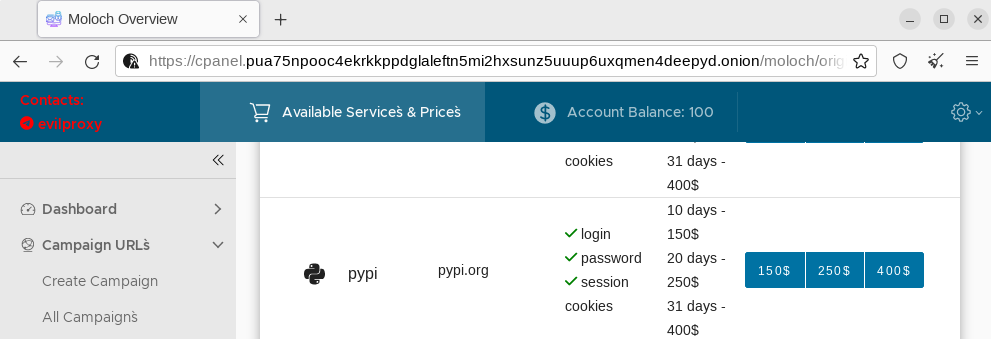
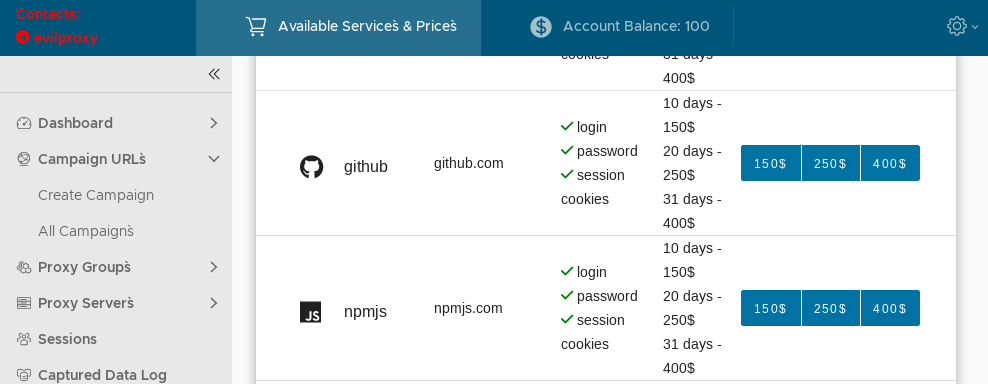
Notably, EvilProxy also supports phishing attacks against Python Package Index (PyPi):
The official software repository for the Python language (Python Package Index (PyPI)) has been recently said (last week) that project contributors were subject to a phishing attack that attempted to trick them into divulging their account login credentials. The attack leveraged JuiceStealer (as the final payload after the initial compromise) and according to Resecurity's HUNTER team findings - related to EvilProxy actors who added this function not too long before the attack was conducted.
Besides PyPi, the functionality of EvilProxy also supports GitHub and npmjs (widely used JavaScript Package Manager by over 11 million developers worldwide) enabling supply chain attacks via advanced phishing campaigns. It's highly likely the actors aim to target software developers and IT engineers to gain access to their repositories with the end goal to hack "downstream" targets. These tactics allow cybercriminals to capitalize on the end users insecurity who assume they're downloading software packages from secure resources and don't expect it to be compromised.
How it works?
EvilProxy uses the “Reverse Proxy” principle. The reverse proxy concept is simple: the bad actors lead victims into a phishing page, use the reverse proxy to fetch all the legitimate content which the user expects including login pages - it sniffs their traffic as it passes through the proxy. This way they can harvest valid session cookies and bypass the need to authenticate with usernames, passwords and/or 2FA tokens.
Resecurity has acquired videos released by EvilProxy actors demonstrating how it can be used to steal the victim’s session and successfully go through Microsoft 2FA and Google e-mail services to gain access to the target account.
Google 2FA
Microsft 2FA
EvilProxy is offered on a subscription base, when the end user (a cybercriminal) chooses a service of interest to target (e.g., Facebook or Linkedin), the activation will be for a specific period of time (10, 20 or 31 days as per the plans description which was published by the actors on multiple Dark Web forums). One of the key actors - John_Malkovich, acting as administrator to vet new customers. The service is represented on all major underground communities including XSS, Exploit and Breached.
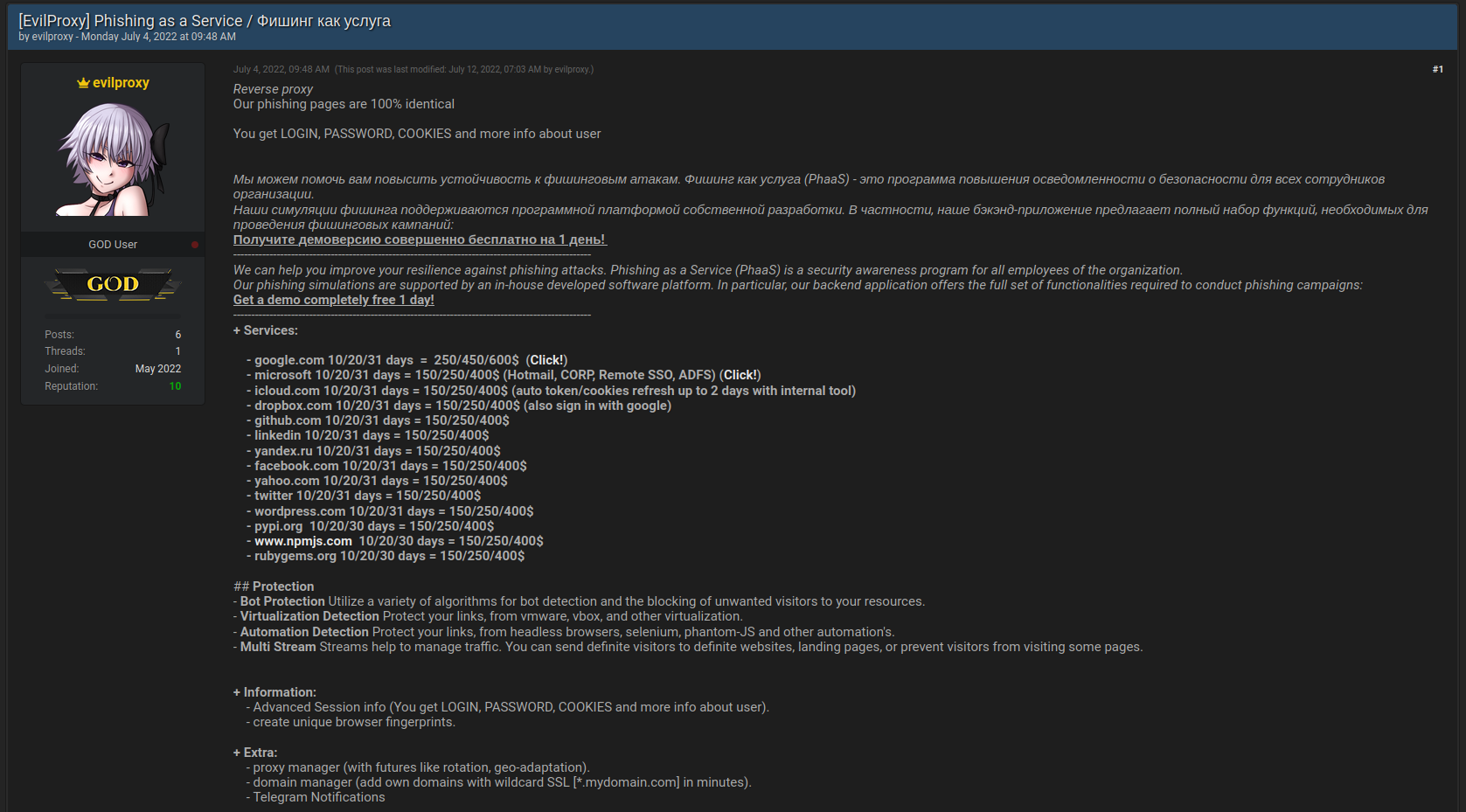
The payment for EvilProxy is organized manually via an operator on Telegram. Once the funds for the subscription are received, they will deposit to the account in customer portal hosted in TOR. The kit is available for $400 per month in the Dark Web hosted in TOR network.
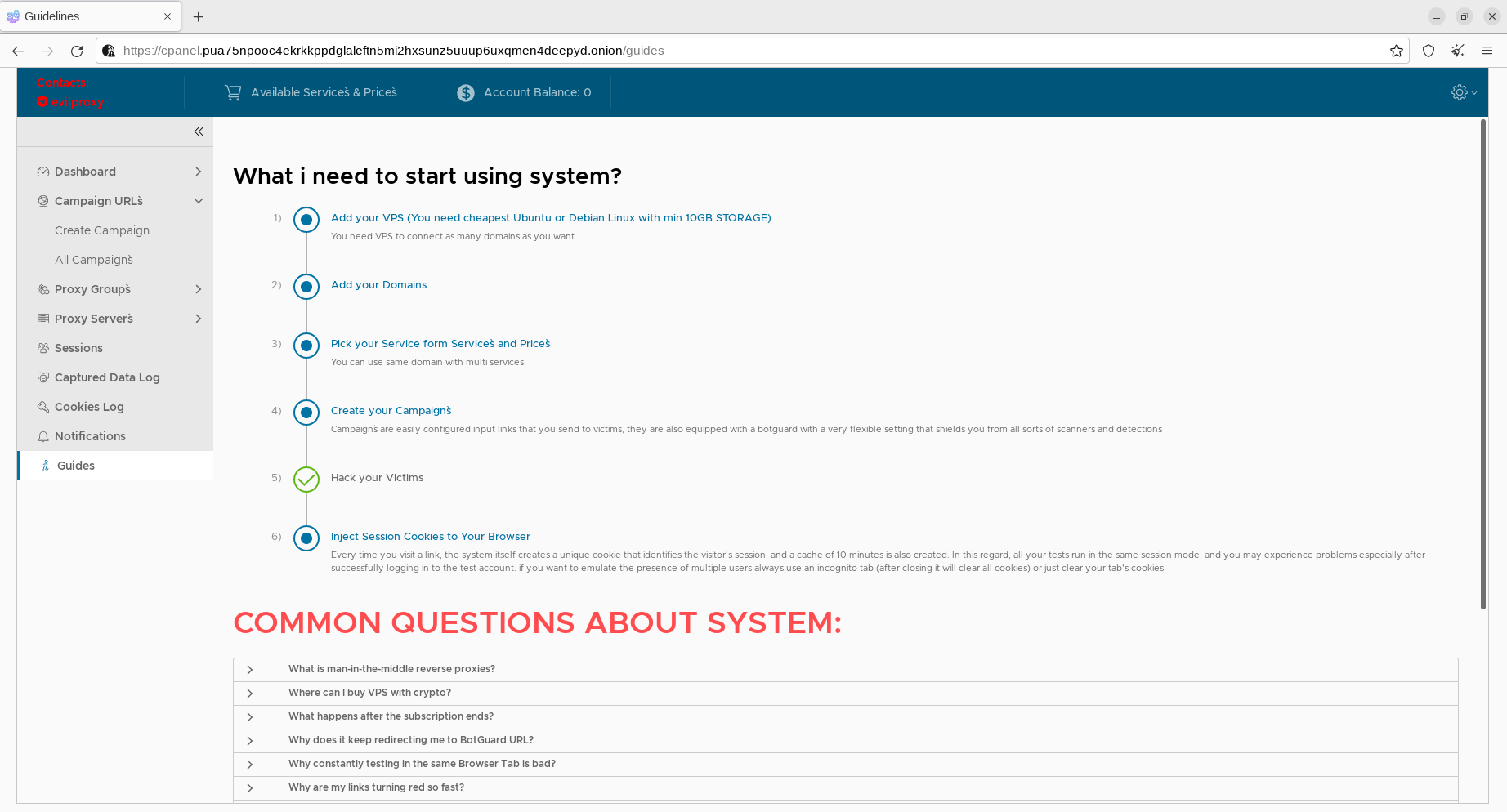
The portal of EvilProxy contains multiple tutorials and interactive videos regarding the use of the service and configuration tips. Being frank – the bad actors did a great job in terms of the service usability, and configurability of new campaigns, traffic flows, and data collection.
After activation, the operator will be asked to provide SSH credentials to further deploy a Docker container and a set of scripts. This approach has also been used in other Phaas service called "Frappo" which was identified by Resecurity this year. The automated installer has a reference to a user "Olf Dobs" (ksh8h297aydO) on Gitlab:
apt update -qqy && apt dist-upgrade --no-install-recommends --no-install-suggests -o Dpkg::options::="--force-confdef" -y \ && apt install --no-install-recommends --no-install-suggests -y git \ && rm -rf /srv/control-agent && git clone --recurse-submodules https://gitlab.com/ksh8h297ayd0/docker-control-agent.git /srv/control-agent \ && cd /srv/control-agent && chmod +x ./install.sh \ && /srv/control-agent/install.sh '[license_key]' ===*=
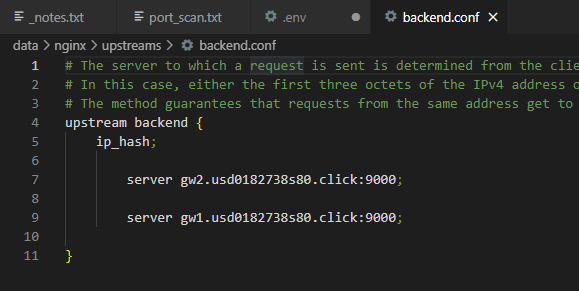
After a successful deployment, the scripts will forward the traffic from the victims via 2 gateways defined as "upstream":
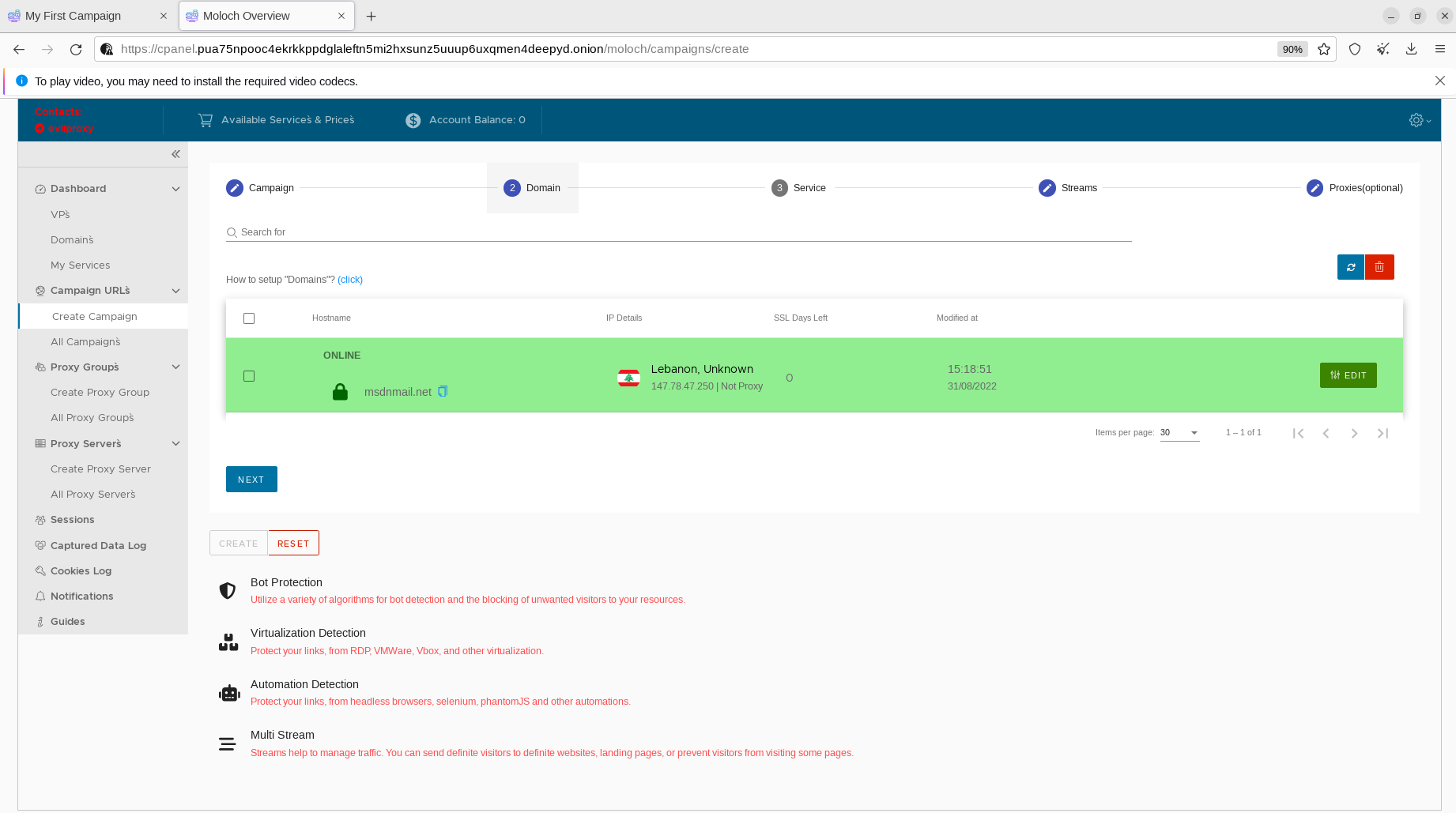
Based on further analysis, we identified some of the domain names used for phishing campaigns. The bad actors register similar (by spelling) domains with the intention of masking them under legitimate online-services.
Some of the links generated by EvilProxy to impersonate Microsoft E-Mail services are provided below:
Login Phishing URL
https://lmo.msdnmail[.]net/common/oauth2/v2.0/authorize?client_id=4765445b-32c6-49b0-83e6-1d93765276ca&redirect_uri=https%3A%2Fopenid%20profile%20https%3
A%2F%2Fwwwofc.msdnmail.net%2Fv2%2FOfficeHome.All&response_mode=form_post&nonce=637975588496970710
.Zjg3YzFkMmEtYTUxYy00NDliLWEzYzAtMTExZTliNjBkY2ZkY2U3NzM2MDMtZWNhZC00ZWFmLWE5YjMtYzgzZTFjM2E1ZDdl&ui_locales=en-US&mkt=en-US&state=jHi-CP0Nu4oFHIxklcT1adstnCWbwJwuXQWTxNSSsw-23qiXK-6EzyYoAyNZ6rHuHwsIYSkRp99F-bqPqhN4JVCnT4-3MQIDvdTKapKarcqaMFi6_xv2__3D0KfqBQ070ykGBGlwxFQ6Mzt9CwUsz2zdgcB4jFux2BhZQwcj-WumSBz0VQs5VePV-wz00E8rDxEXfQdlv-AT29EwdG77AmGWinyf3yQXSZTHJyo8s-IWSHoly3Kbturwnc87sDC3uwEn6VDIjKbbaJ-c-WOzrg&x-client-SKU=ID_NETSTANDARD2_0&x-client-ver=6.16.0.0
Post-Authorization URL
https://473126b6-bf9a-4a96-8111-fb04f6631ad8-571c4b21.msdnmail[.]net/mail/?realm=[victim_domain]&exsvurl=1&ll-cc=1033&modurl=0&JitExp=1&url=%2Fowa%2F%3Frealm%253d%2526exsvurl%253d1%2526ll-cc%253d1033%2526modurl%253d0%2526login_hint%253[victim_email]%252540[victim_domain]
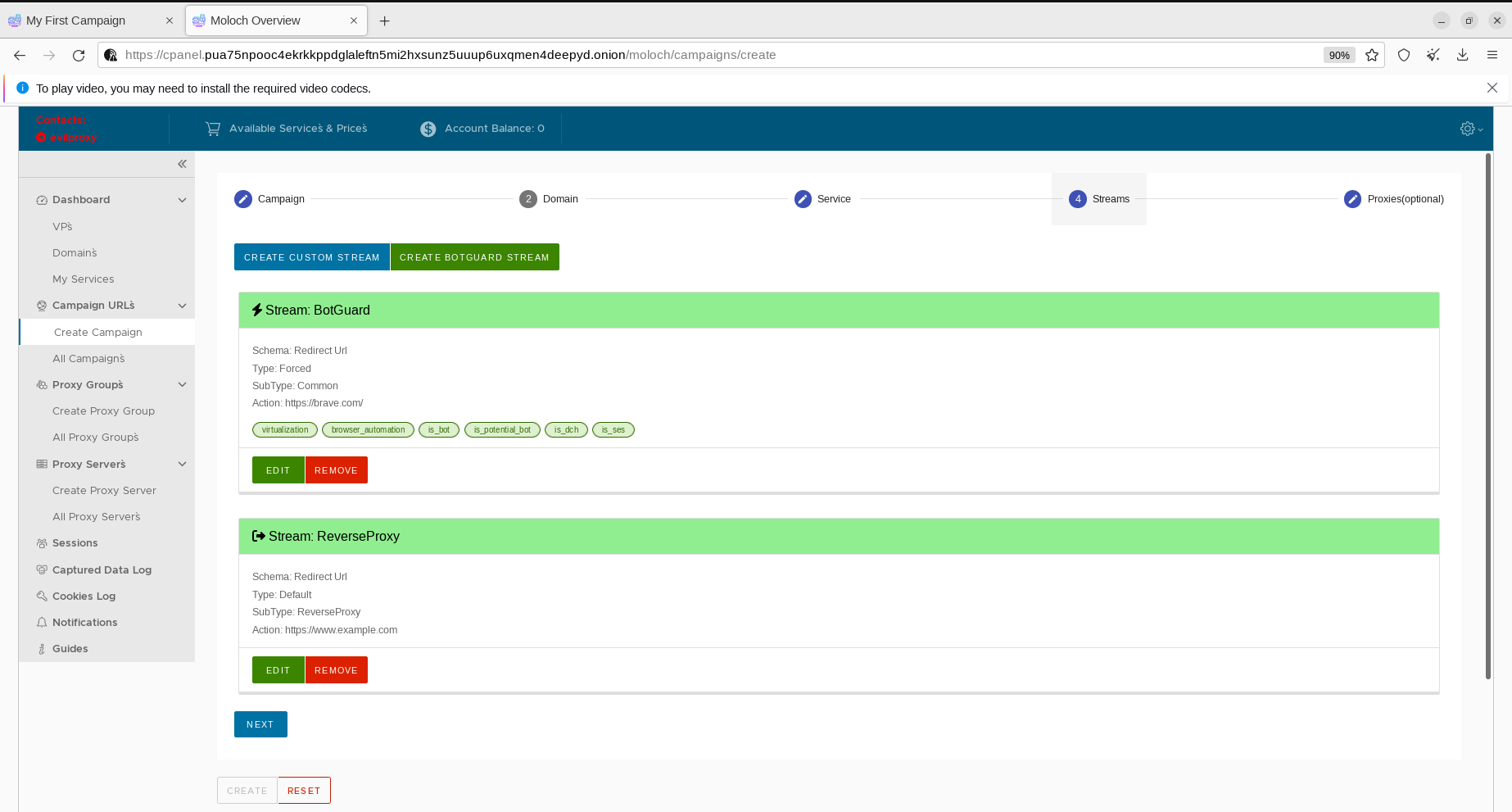
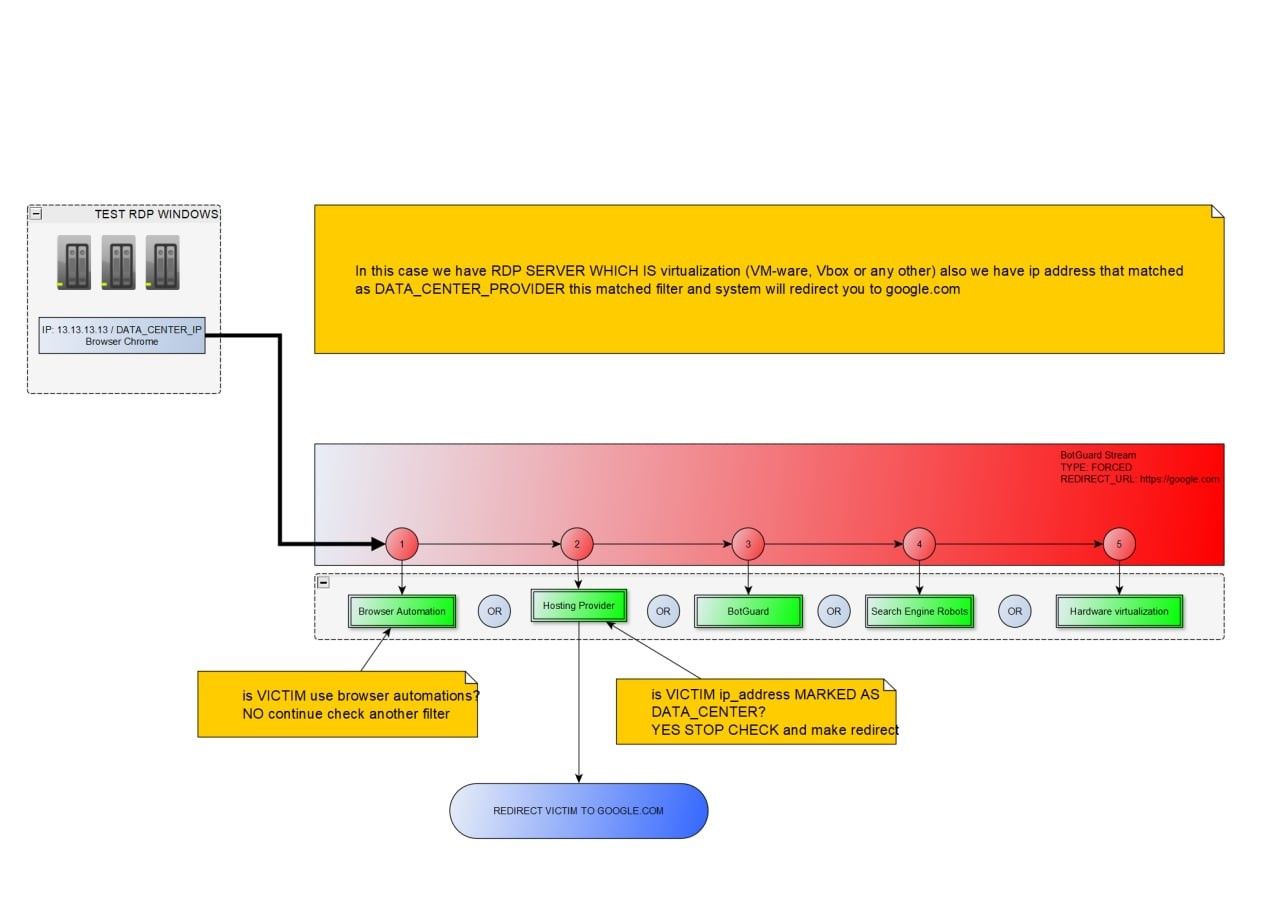
The bad actors are using multiple techniques and approaches to recognize victims and to protect the phishing-kit code from being detected. Like fraud prevention and cyber threat intelligence (CTI) solutions, they aggregate data about known VPN services, Proxies, TOR exit nodes and other hosts which may be used for IP reputation analysis (of potential victims). In the case they suspect a bot or researcher, they drop the connection or redirect it to a specific host (for example, ‘brave.com’).
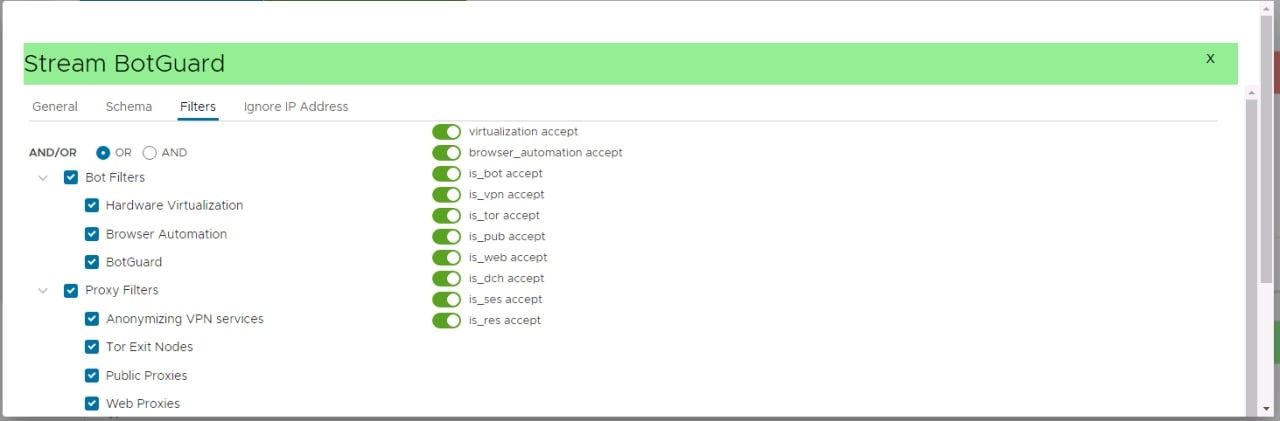
Another approach which has been identified is based on fingerprints.
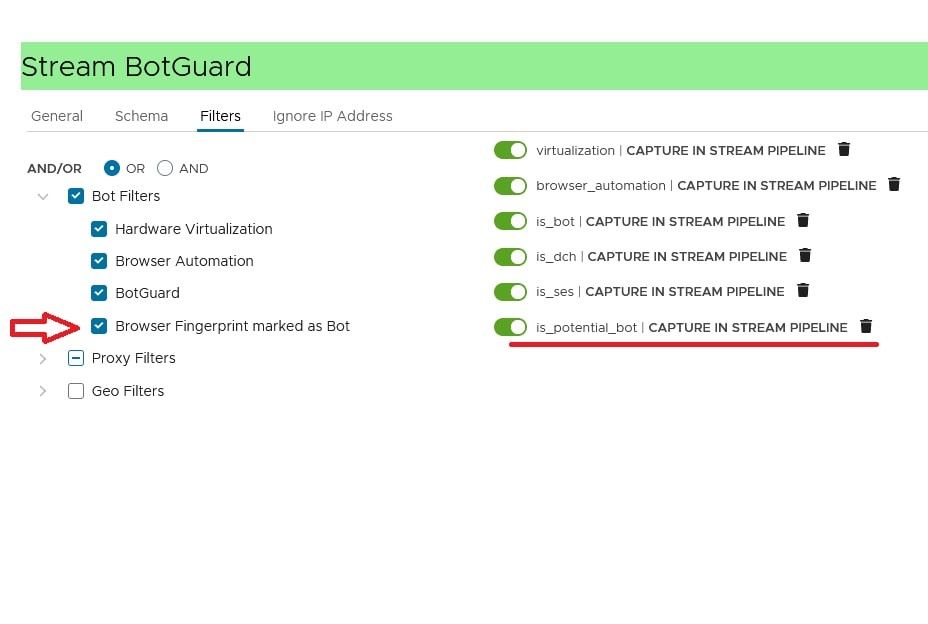
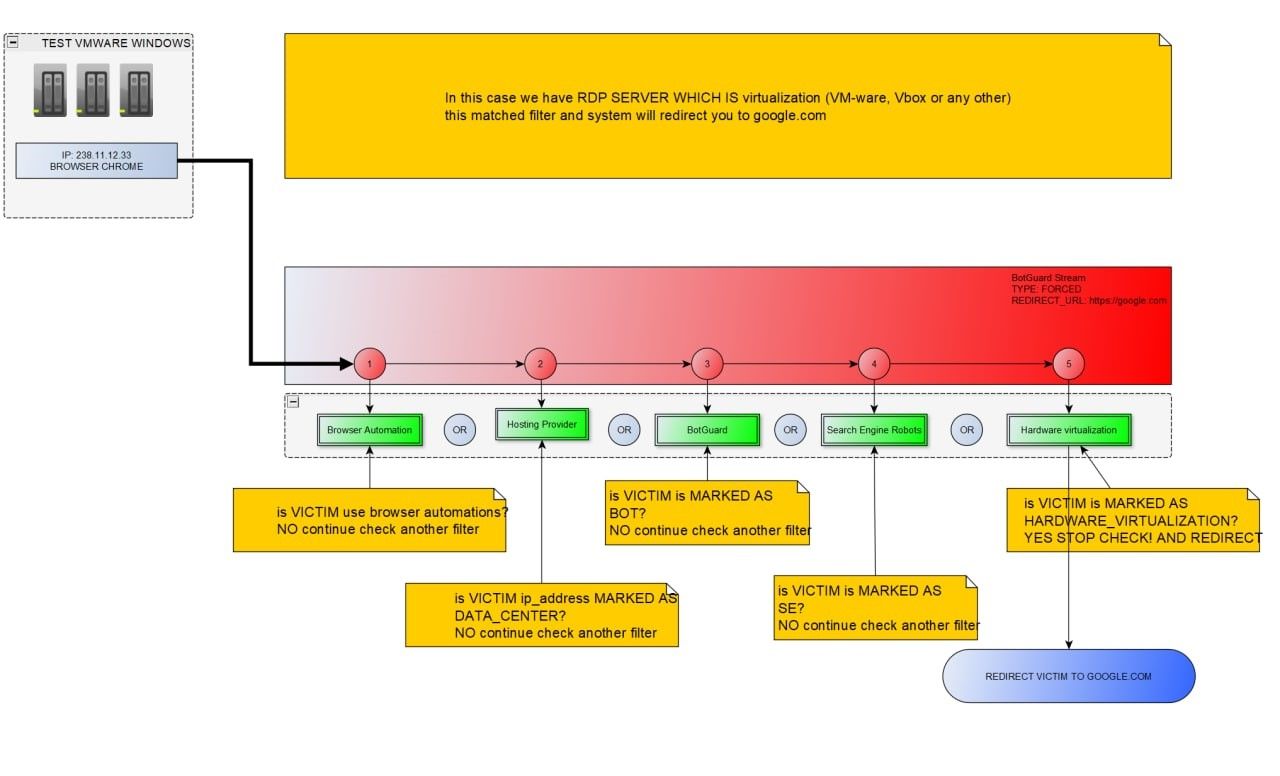
The bad actors are especially diligent when it comes to detecting possible virtual machines, typically used by security analysts to research malicious content and clients connecting via RDP (Remote Desktop Protocol):
Significance
While the sale of EvilProxy requires vetting, cybercriminals now have a cost-effective and scalable solution to perform advanced phishing attacks to compromise consumers of popular online services with enabled MFA. The appearance of such services in Dark Web will lead to a significant increase in ATO/BEC activity and cyberattacks targeting the identity of the end users, where MFA may be easily bypassed with the help of tools like EvilProxy.
IOC:
Resecurity’s HUNTER team collected the following domain names and URLs related to the EvilProxy infrastructure. Some of these hosts were mapped as a result of post-incident response engagement with the affected victims from Fortune 500 companies and consumers of popular online-services. While the operations of bad actors are extremely dynamic, the information about these hosts may help cybersecurity researchers and incident responders detect and attribute possible malicious activity to EvilProxy when investigating incidents affecting MFA (2FA).
- 147[.]78[.]47[.]250
- 185[.]158[.]251[.]169
- 194[.]76[.]226[.]166
- msdnmail[.]net
- evilproxy[.]pro
- top-cyber[.]club
- rproxy[.]io
- login-live.rproxy[.]io
- gw1.usd0182738s80[.]click:9000
- gw2.usd0182738s80[.]click:9000
- cpanel.evilproxy[.]pro
- cpanel.pua75npooc4ekrkkppdglaleftn5mi2hxsunz5uuup6uxqmen4deepyd[.]onion

