Smishing Triad is Now Targeting Toll Payment Services in a Massive Fraud Campaign Expansion
Fraud Intelligence

The Spring Refresh
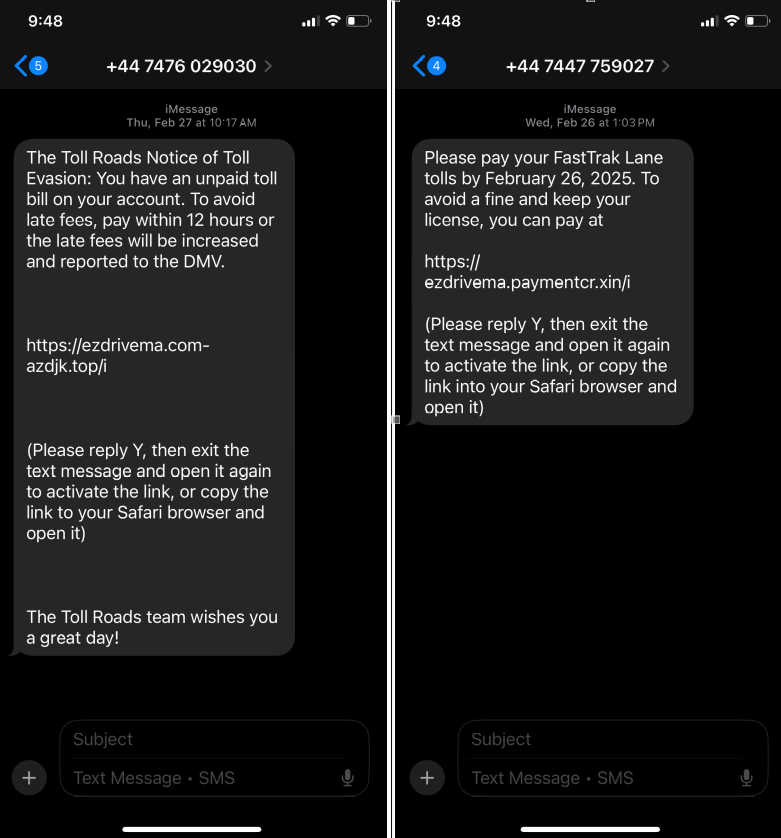
The Smishing Triad, a China-based cybercriminal group, has been linked to a surge in smishing campaigns targeting US and UK consumers. These campaigns involve fraudulent text messages claiming unpaid toll bills or payment requests related to toll services like FasTrak, E-ZPass, and I-Pass, which is expected to expand to similar services worldwide as their earlier campaigns did.
These techniques are challenging for consumers to mitigate because actors are impersonating legitimate organizations by spoofing Senders ID (SID). They also leverage SMS, iMessage, and similar instant messaging apps (collectively called IM messages for this blog) that have reduced spam protection compared to email service providers. End users place more trust in these types of messages than in email, and these messages also create a sense of urgency for users to resolve the issue. This results in a significantly higher expected conversion rate than email, SEO, and other techniques the actors could use.
The scam involves sending IM messages that appear to come from legitimate tolling agencies. These messages demand payment for supposed unpaid tolls or request sensitive information. The goal is not only to extract money but also to steal personal and financial information from victims for future victimization.
The campaign has utilized over 60,000 domain names, making it difficult for platforms like Apple and Android to block fraudulent activity effectively. A significant spike in these activities was observed at the beginning of Q1 2025, with millions of consumers targeted. Some malicious texts have been sent from UK numbers leveraging underground bulk IM/SMS services.
Notably, some of the identified domain names were registered in the ".xin" top-level domain (gTLD), which translates to "new" or "faith" in Chinese. Elegant Leader Limited manages this domain, which is aimed at Chinese language users, particularly for new or innovative organizations.
According to the description of the .XIN, the zone is managed out of Hong Kong, China:
Sponsoring Organization
Elegant Leader Limited
25/F Jubilee Centre
18 Fenwick Street
Wanchai
Hong Kong
China
Administrative Contact
Fuping Yu
Elegant Leader Limited
31/F., Tower One, Times Square, 1 Matheson Street
Causeway Bay
Hong Kong
Email: yufuping.yfp@alibaba-inc.com
Voice: +86 10 65985888 ext. 49971
Fax: +86 10 65985608
Technical Contact
Senior Director, DNS Infrastructure Group
Afilias (owned by Identity.Digital)
300 Welsh Road
Building 3, Suite 105
Horsham PA 19044
United States of America (the)
Email: tld-tech-poc@afilias.info
Voice: +1 215.706.5700
Fax: +1 215.706.5701
Federal and state agencies have warned about these scams, urging individuals to verify toll-related claims through official websites. Consumers are advised not to click on links in unsolicited text messages and to report suspicious messages to authorities.
The notable detail of this activity, besides leveraging iMessage to send smishing content to Apple device users and RCS to Android users, is that the group seems to be utilizing SMS gateways and routes that are either leased or purchased and registered under various business entities operating as 'marketing companies'.
Underground Bulk SMS Services
Using underground bulk SMS services enables cybercriminals to scale their operations, targeting millions of users simultaneously. These services allow attackers to efficiently send thousands or millions of fraudulent IM messages, targeting users individually or groups of users based on specific demographics across various regions.
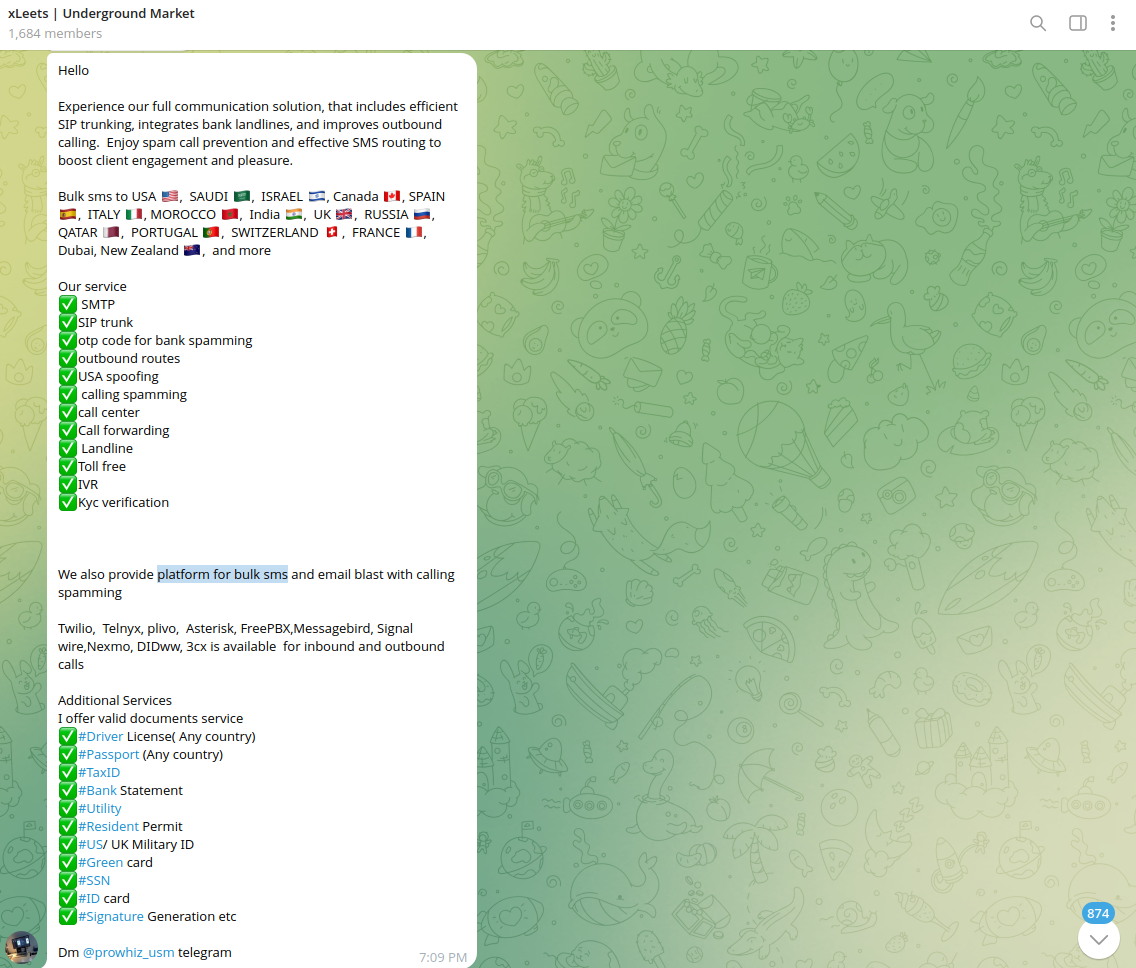
Such underground vendors provide the infrastructure to send millions of malicious IM messages at scale. These messages often include links to fraudulent websites mimicking legitimate entities such as banks, payment systems, and other online services.
Cybercriminals send IM messages that appear to come from legitimate banks. These messages often use spoofed sender IDs, making them appear from the bank's official number.
For example, these scams are designed to exploit victims' trust in financial institutions and IM messages by creating a sense of urgency and fear, prompting them to take immediate action.
Victims are instructed to either:
- Call a provided phone number connecting them to the scammers posing as bank representatives.
- Click on a link that leads to a phishing website mimicking the bank's official site.
Once the victim calls or clicks the link, they are asked to provide sensitive information such as account credentials, credit card details, or personal identification information (PII). This data is then used for immediate and future financial fraud or identity theft.
Cybercriminals are increasingly utilizing a combination of ranges of phone numbers and targeted databases built from stolen consumer data obtained through data breaches. This approach improves the effectiveness of their smishing campaigns, enabling them to reach potential victims more efficiently while minimizing the chances of detection by an IM or carrier’s spam filter. Campaigns that utilize targeted consumer data tend to have higher success rates, as they can craft messages that resonate more with the recipients. For example, a message referencing a recent transaction or account activity can create a sense of urgency. Based on observed statistics, actors send thousands of daily smishing messages, leveraging underground vendors.
Such service delivery on the Dark Web may vary. In some cases, the actors provide actual access to an already configured SMS gateway (available for rent) or a web interface to create new campaigns.
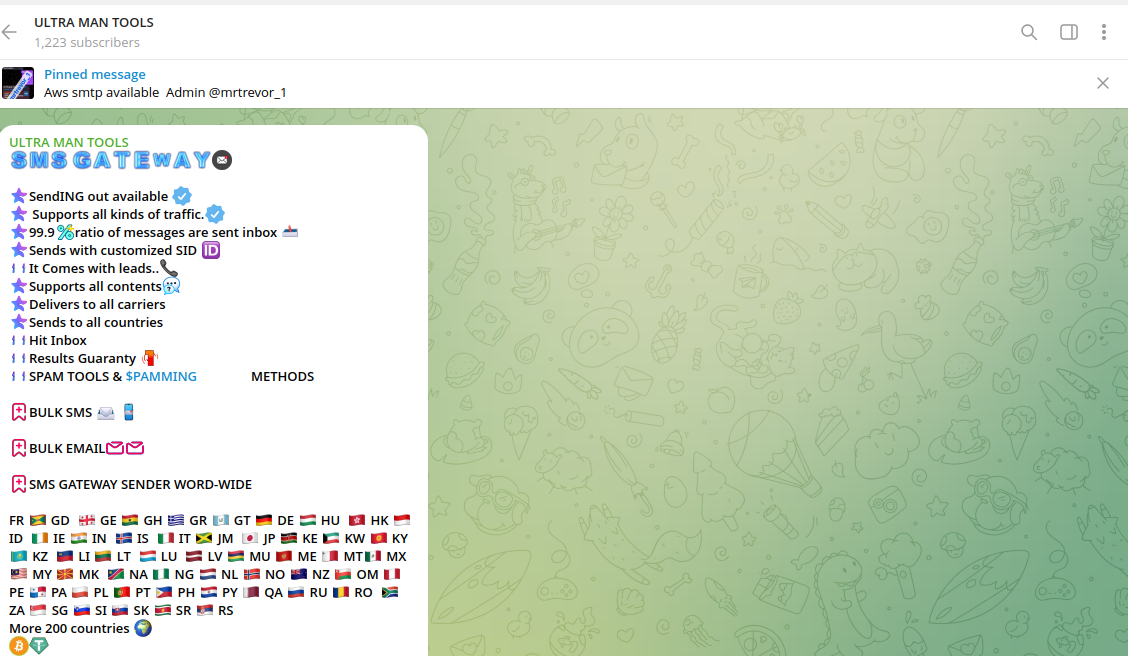
Compared to legitimate bulk IM providers, such underground services offer the opportunity to modify the Sender ID (SID) and include fraudulent links in the body of the message. The actors' goal is to provoke the victim to respond or click on the URL by seeing a notification from a popular service. Cybercriminals call this "generating traffic," as they are not interested in a specific victim and aim to defraud many consumers. That's why they use SIDs to impersonate popular services like Binance, Netflix, e-government applications, etc.

The victim will receive SMS notifications that appear to be sent by legitimate services, such as the cryptocurrency platform Binance, alerting them about possible fraud and the need to confirm their OTP.

The price for such underground services varies and depends on the region. For example, sending 1,000 smishing messages to UK consumers will cost around $8.00.
Oak Tel from China - The Catalyst of Global Smishing
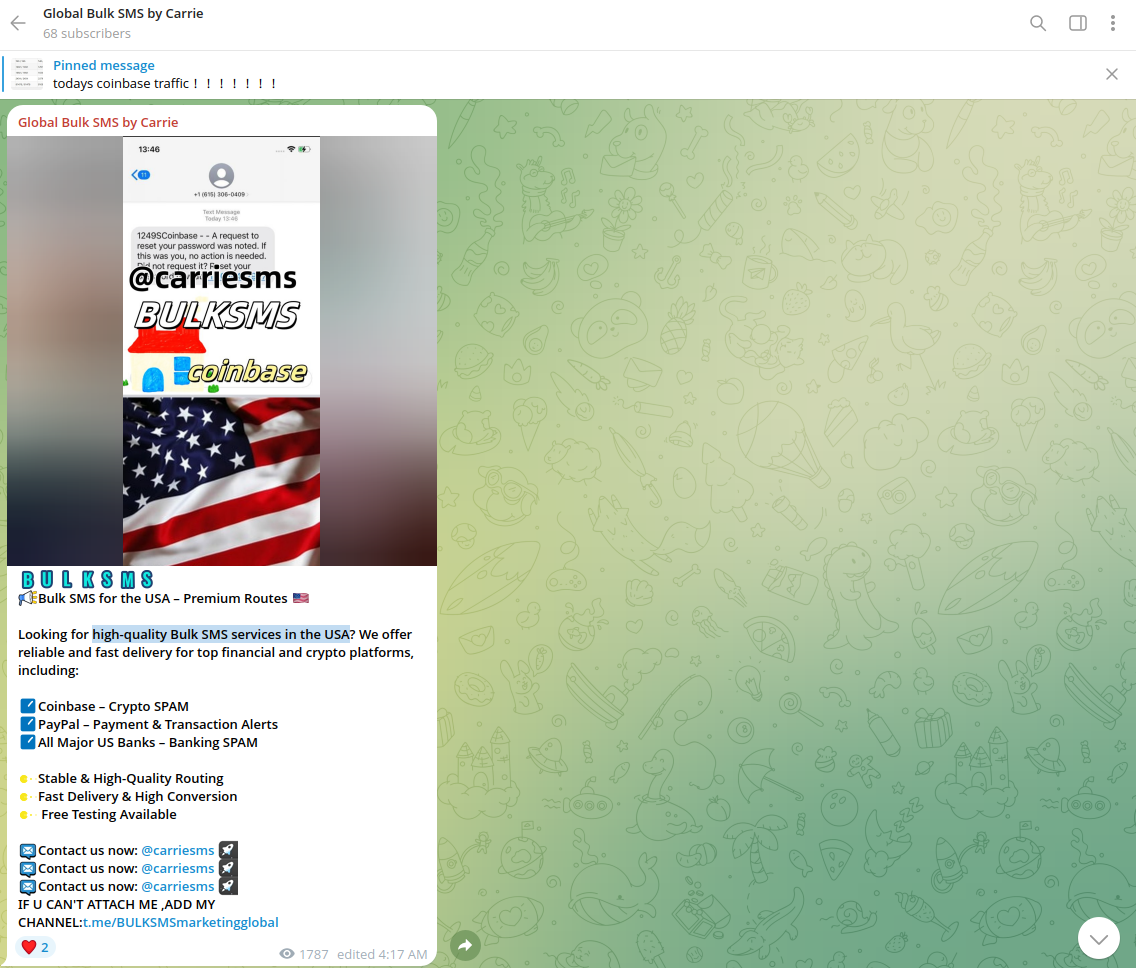
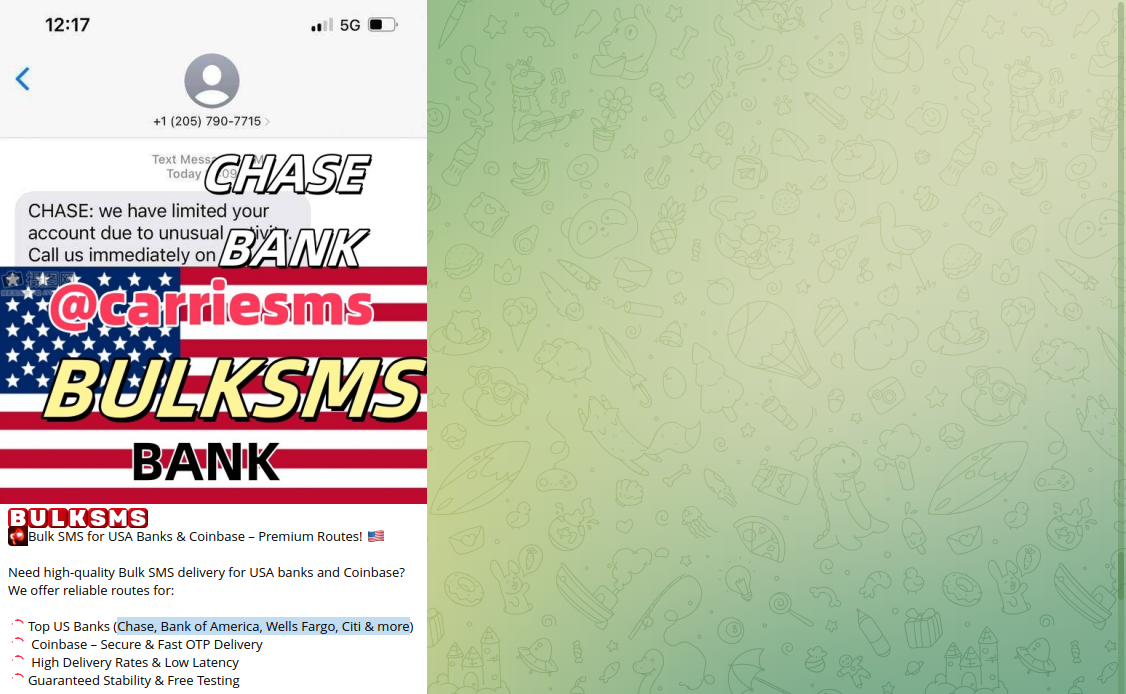
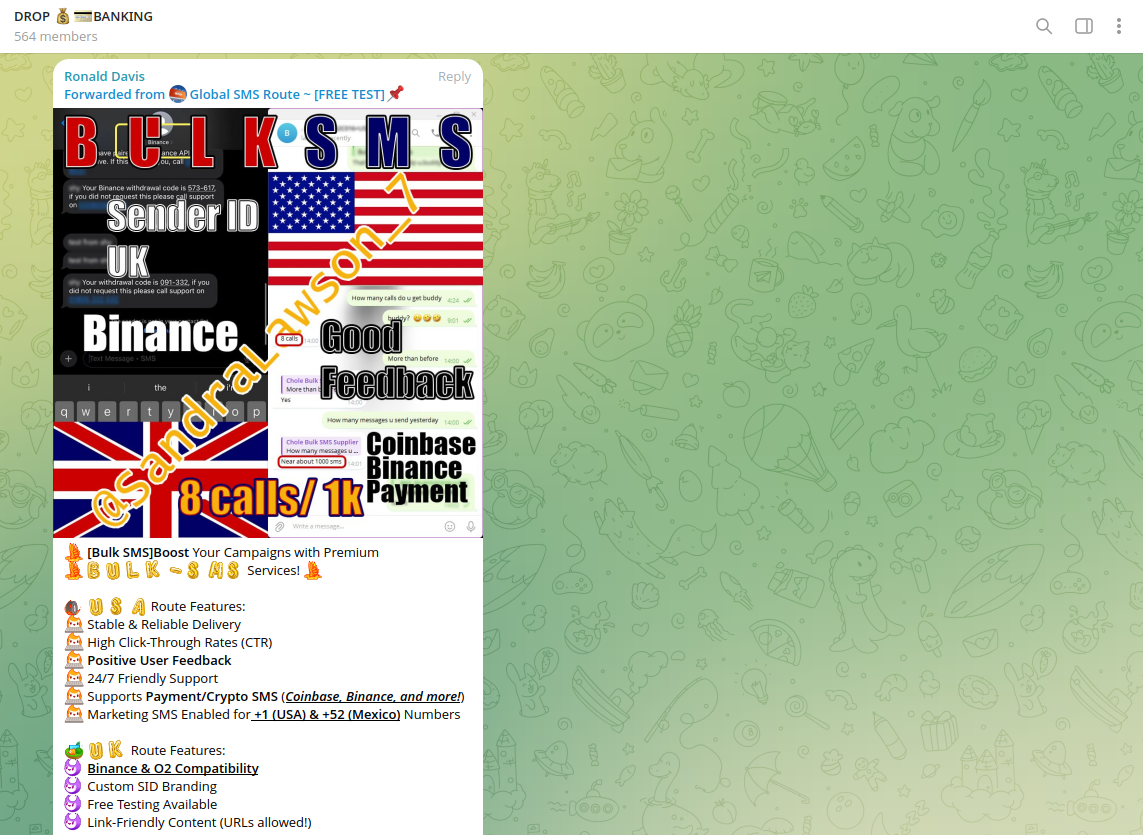
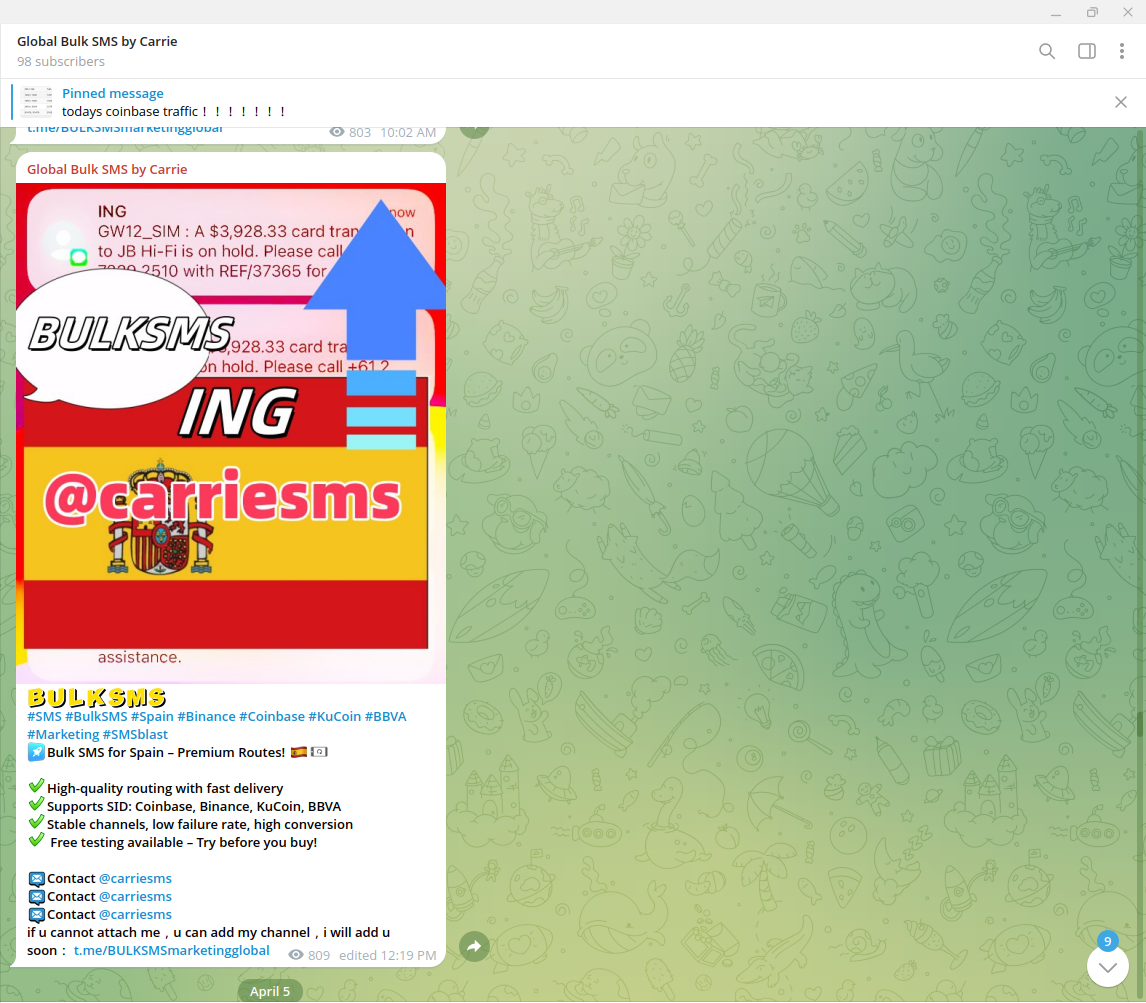
Resecurity identified an underground bulk IM service called "Oak Tel," frequently used by the group and other cyber criminals involved in smishing. The service is also known using the alternative alias "Carrie SMS," supporting the SIDs of many US-based financial institutions, including Chase, Bank of America, Wells Fargo, and Citi.
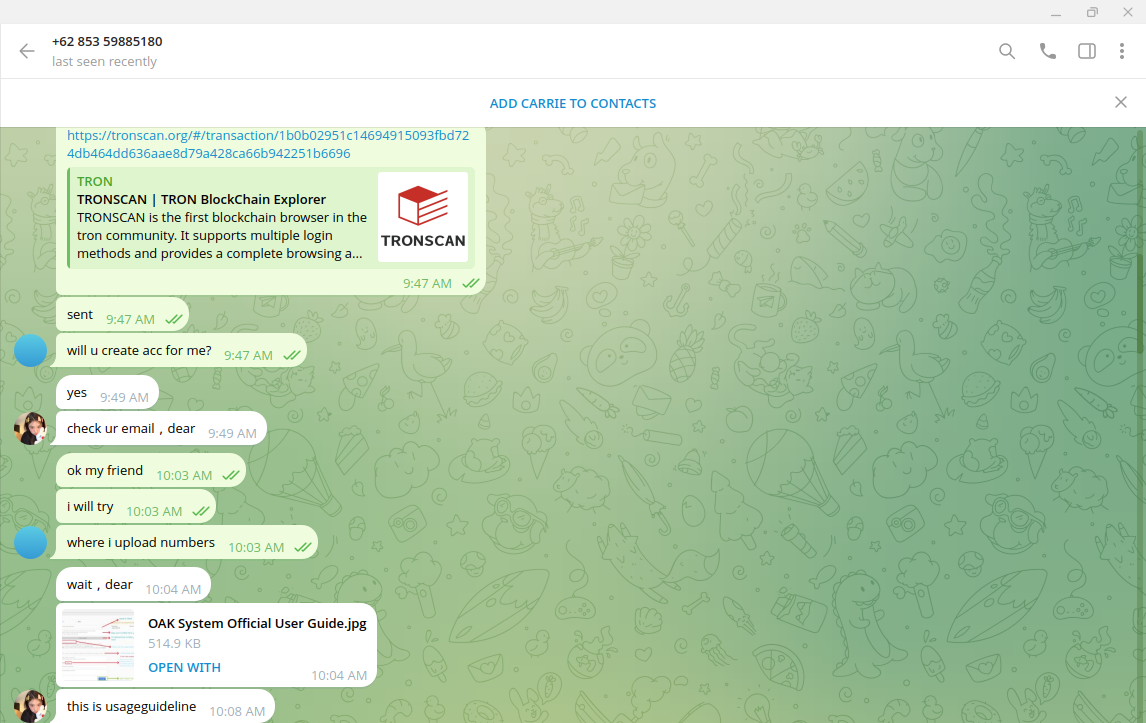
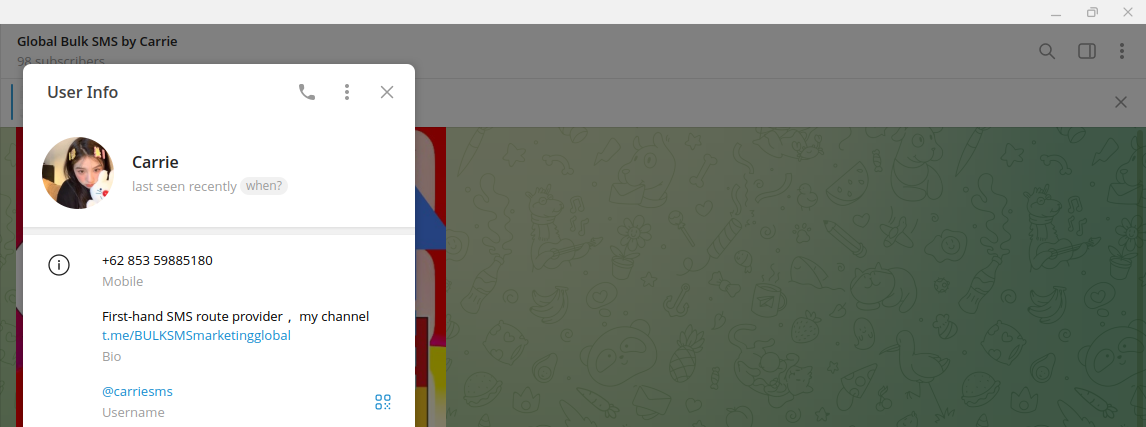
Once paid, cybercriminals provide access to a web panel to manage a new campaign hosted at oak-tel[.]com. The service is provided by an actor in Telegram under the alias "Carrie" using the phone number +62 853 59885180 (Indonesia).
Our investigators arranged a cryptocurrency transfer as requested by "Carrie" and received a manual with instructions and an account to access the interactive dashboard for sending bulk SMS.
Notably, the "Carrie" in question states "global marketing services" in her profile on Telegram; however, the nature of her postings clearly indicates that the service is facilitating banking, e-commerce, and crypto-enabled fraud.
For example, the most recent instances of bulk SMS campaigns include the delivery of content impersonating popular cryptocurrency exchanges such as Coinbase, Binance, and KuCoin, as well as banking institutions like BBVA. Additionally, there were fake notifications about the need to contact customer support due to card transactions or transfers that were put on hold. This tactic is widely used by fraudsters in social engineering activities to trick victims into disclosing sensitive information by impersonating customer support.
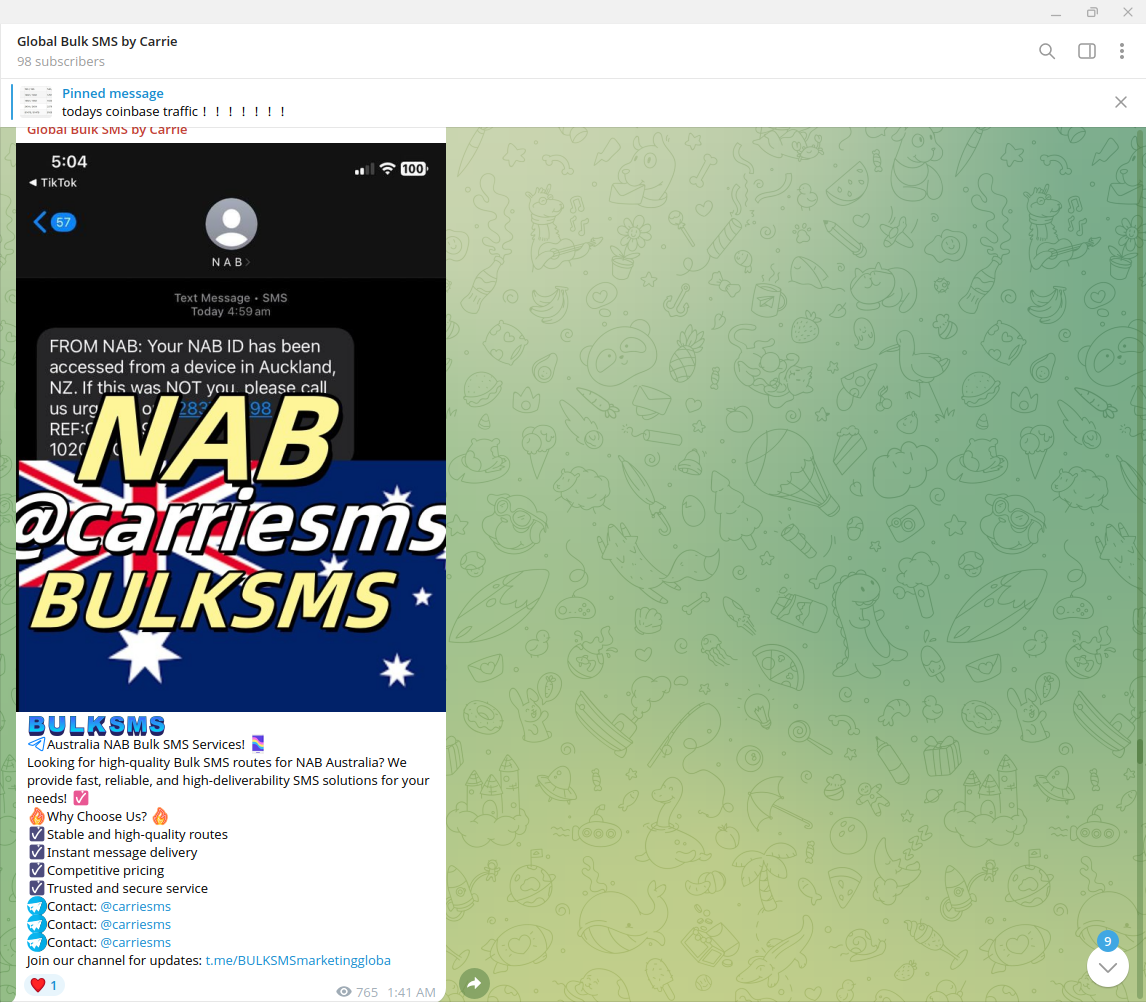
In another example, the same actor shared a fake notification designed for delivery to customers of the National Australia Bank (NAB), provoking them to contact a specific phone number that is not associated with the bank. As a pretext, the fraudster alerts them about a possible account compromise and the urgent need to contact customer support. The fraudster will later ask specific questions to leverage the trust of the victim for identity theft and confirmation of the OTP to facilitate unauthorized access to the account.
Obviously, such tactics are significantly different from traditional marketing and cannot be interpreted as intended for legitimate purposes.At the same time, there is a risk associated with other bulk SMS services when fraudsters abuse their existing policies and misuse their
infrastructure.
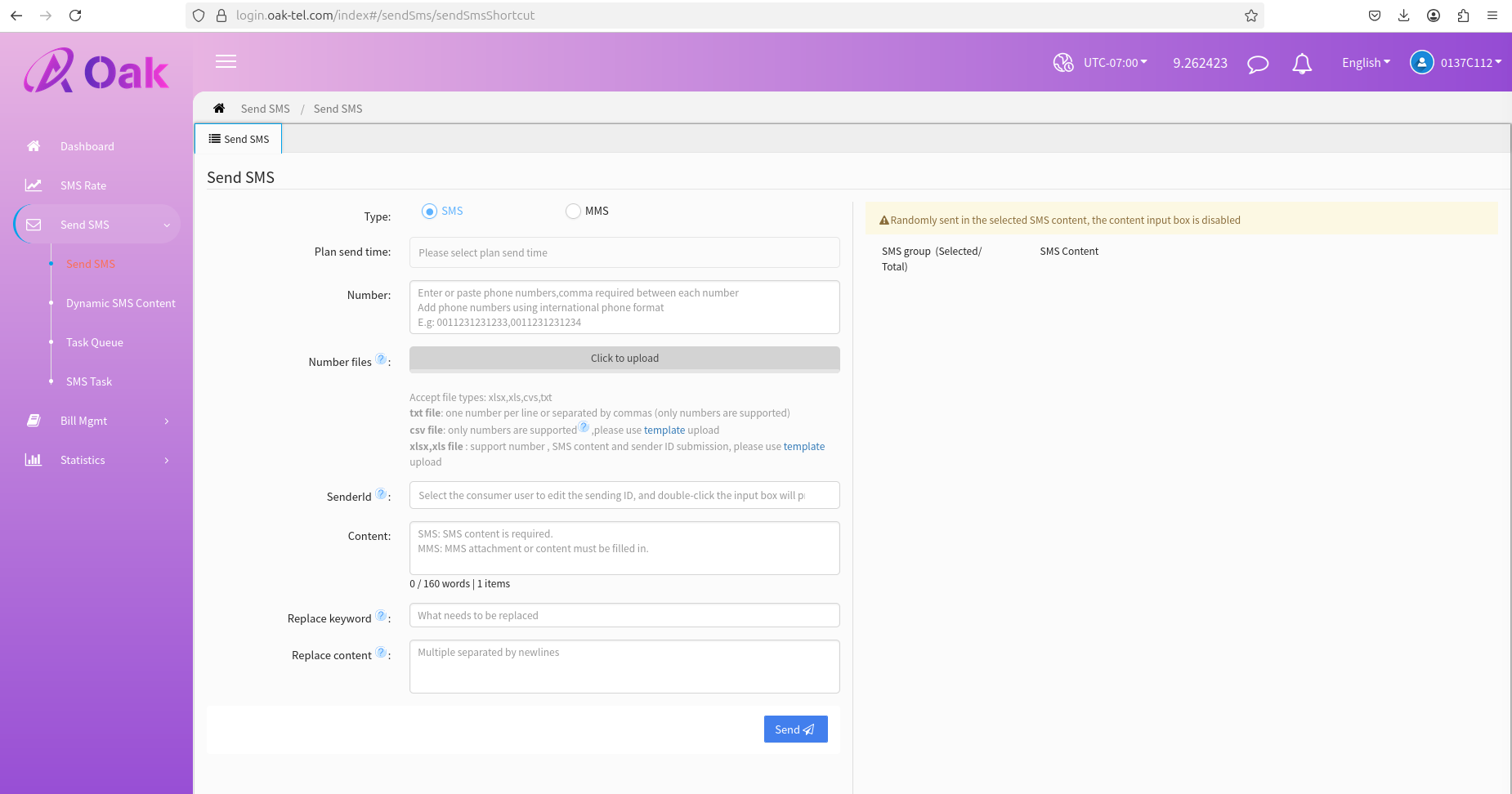
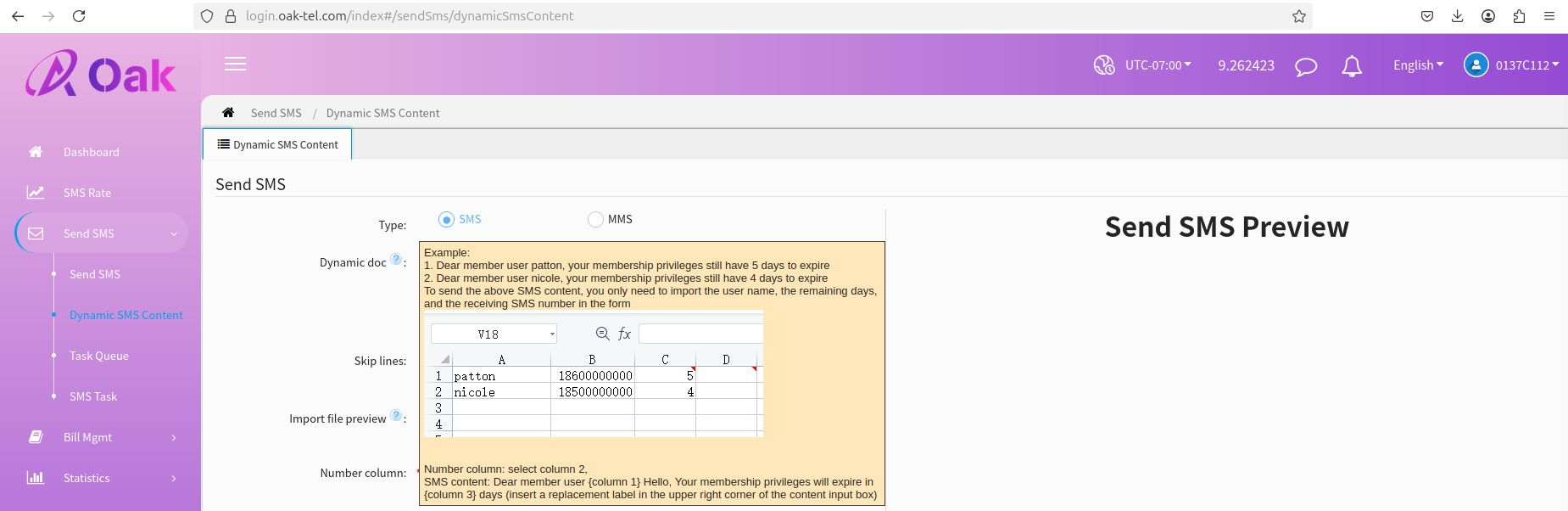
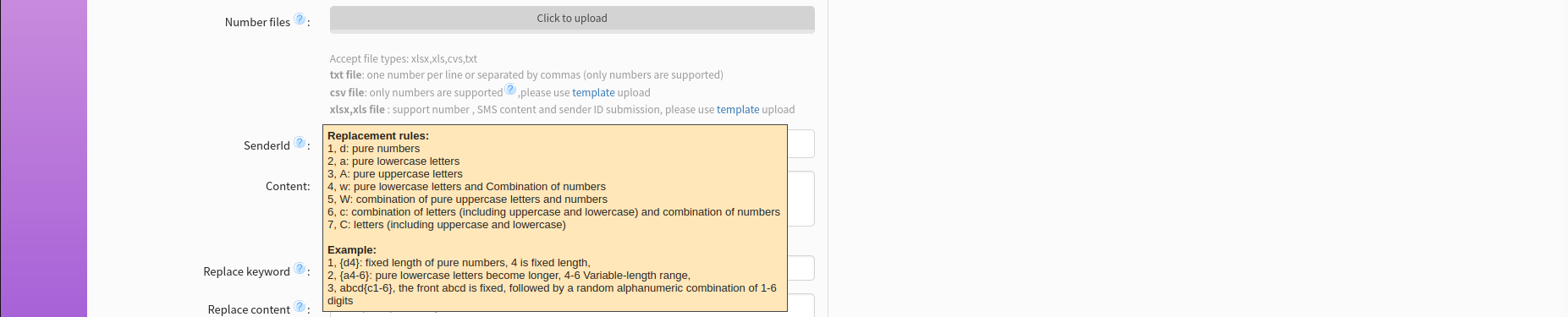
Operators may configure various parameters and prepare different templates to randomize smishing messages. Our investigators acquired access to one of such services called "Oak Tel" managed by actors in China:
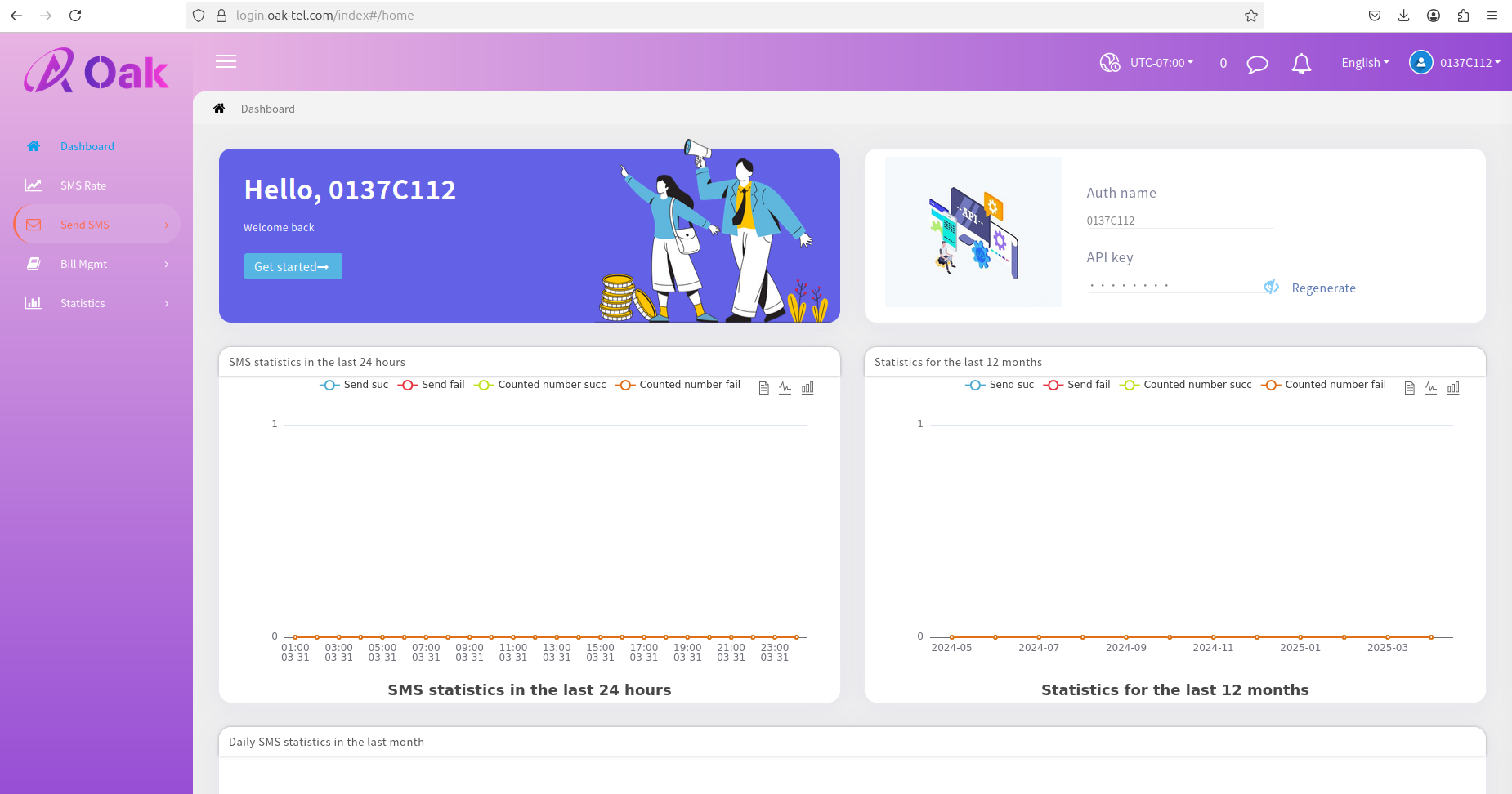
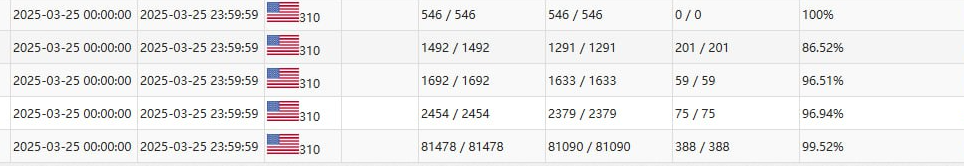
The portal provides API and a mechanism to track statistics on sent/failed messages:
The operator may create multiple smishing campaigns randomizing content and tracking their campaign’s status from a dashboard:
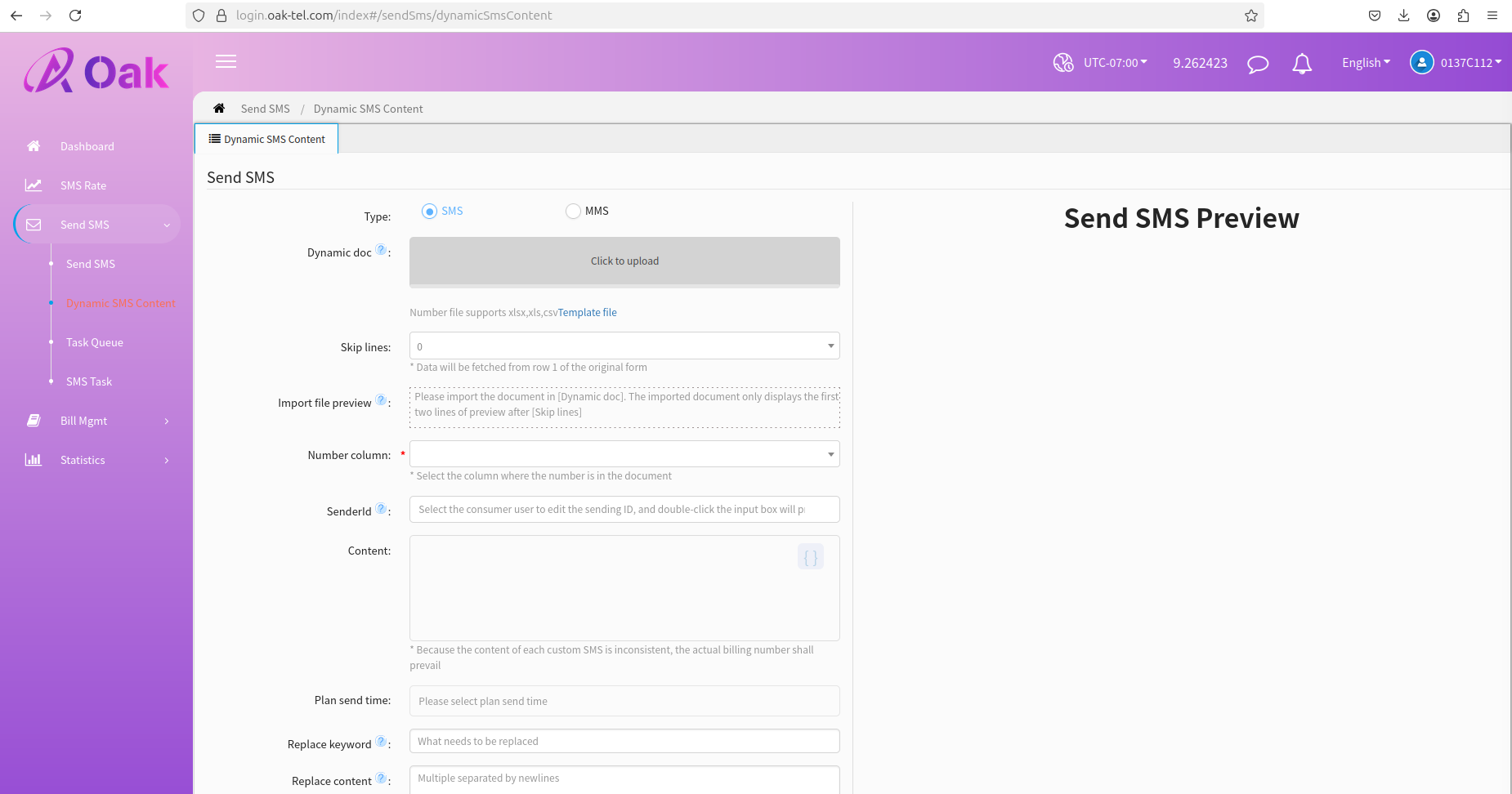
The service allows for creating dynamic SMS content, in which the victim is asked to enter various codes or commands (press "1" for ...).
The features allow the modification of Sender ID (SID), for example, defining it as "US Postal Service" or "Chase Bank," and uploading the file with victims' phone numbers to send smishing to:
Like domain names used by Smishing Triad, this service has also been registered via Alibaba.
Domain Name: oak-tel.com
Registry Domain ID: 2856821299_DOMAIN_COM-VRSN
Registrar WHOIS Server: grs-whois.hichina.com
Registrar URL: http://wanwang.aliyun.com
Updated Date: 2025-02-21T06:14:08Z
Creation Date: 2024-02-20T03:43:02Z
Registrar Registration Expiration Date: 2026-02-20T03:43:02Z
Registrar: Alibaba Cloud Computing Ltd. d/b/a HiChina (www.net.cn)
Registrar IANA ID: 1599
Reseller:
Domain Status: ok https://icann.org/epp#ok
Registrant City:
Registrant State/Province: Guang Dong
Registrant Country: CN
Registrant Email:https://whois.aliyun.com/whois/whoisForm
Registry Registrant ID: Not Available From Registry
Name Server: DNS10.HICHINA.COM
Name Server: DNS9.HICHINA.COM
DNSSEC: unsigned
Registrar Abuse Contact Email: DomainAbuse@service.aliyun.com
Registrar Abuse Contact Phone: +86.95187
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>>Last update of WHOIS database: 2025-03-31T16:57:13Z <<<
Mitigation Measures
Users
It is challenging for consumers to mitigate smishing because actors have started impersonating legitimate organizations by spoofing sender IDs (SIDs). If you receive a message that appears to be from a bank or service provider, contact them via their official number and make sure their notification is legitimate.
Be wary of messages that create a sense of urgency or ask for personal information. Scammers often use tactics that pressure you to act quickly.
Enable security features on your smartphone, such as spam filters and message blocking, to help reduce the number of smishing attempts you receive.
By following these recommendations, you can significantly reduce your risk of being a victim of smishing attacks and protect your personal information.
IM service providers
Carriers and IM providers must also enhance their spam protection for these messages and incorporate the lessons learned from email spam protection, including throttling, content monitoring, IP and phone number reputation, time-traveling spam mitigation, and more.
Incorporating best practices and adapting them to the unique aspects of IM messaging can significantly increase the cost to the threat actors while decreasing the scale, effectiveness, and conversion rates of attacks that utilize IM services as a key component.

